Versions Supported: Enterprise
VictorOps Version Required: N/A SaaS
The matching condition will determine when this rule should be applied. You can choose any field that exists within the payload of an alert and match on a specific value for that field using a direct match, wildcard matching, or by using a regular expression.
By default the Rules Engine is only enabled for wildcard matching. If you would like to enable the advanced configuration for use with RegEx please contact Splunk On-Call Support.
When viewing an incident in the timeline, field names are on the left and values are on the right:
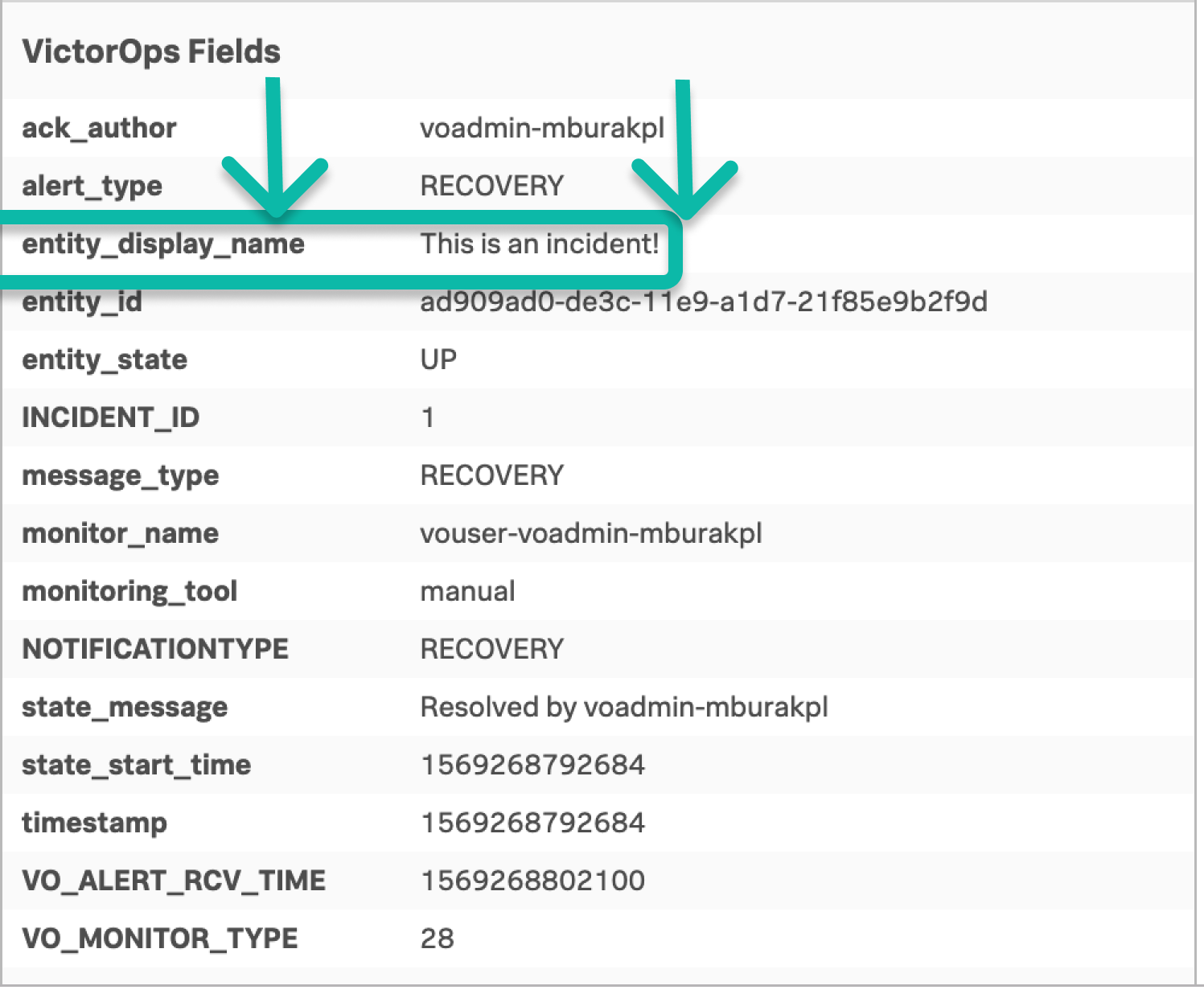
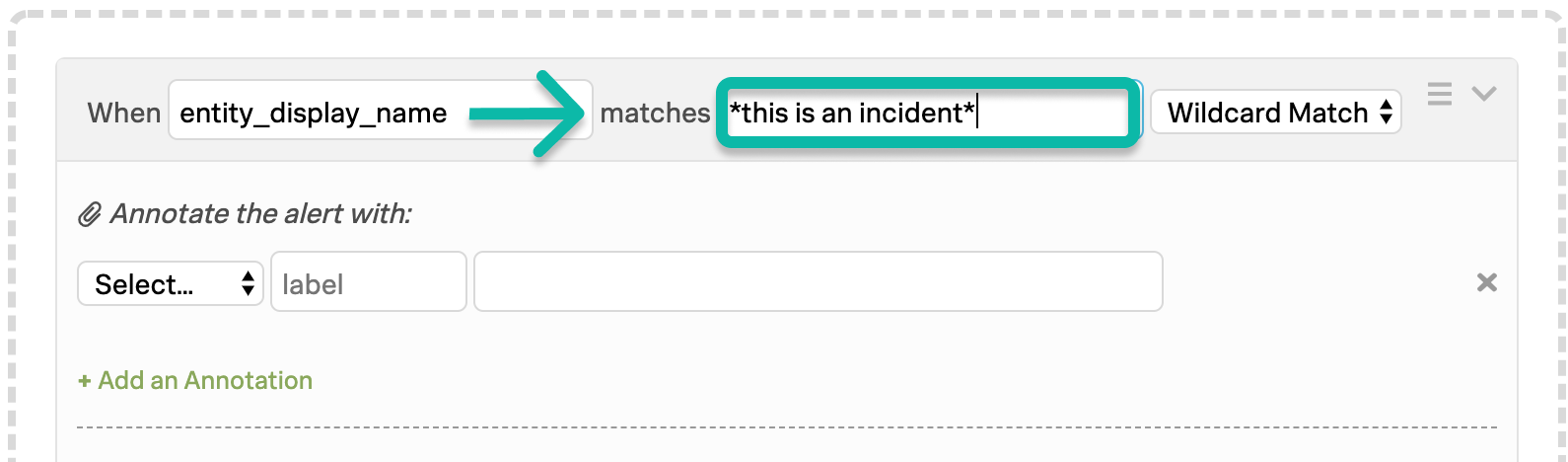
In the above example, the field of interest is the entity_display_name field and the value that matters is the phrase “This is an incident!”. The matching condition, therefore, is the following (wildcard matching used in this example, hence the “*” asterisks).
Wildcard Matching
Rules can match on an alert field value using a simplified wildcard syntax to match some or all of the string. The asterisk “*” character matches 0 or more characters and can be used anywhere in the match pattern.
Wildcard Examples:
| Phrase | Matches | Does Not Match |
|---|---|---|
| *.mydomain.tld | www.mydomain.tld www.subdomain.mydomain.tld db778.mydomain.tld | mydomain.tld x.mydomain.tld/with/a/long/path/suffix.html |
| db-*.* | db-123.foobar.baz db-abc123.bazfoo.bar | db000.barfoo.baz db-123 |
| *db-mydomain* | 123 db-mydomain abc foo-db-mydomain-bar | db123-mydomain db.mydomain |
Matching with Regular Expressions (RegEx)
Regular expressions are characters that define search patterns. To set a rule to use regex, simply change the drop down option to “RegEx Match”. If you do not see the option, please reach out to support to enable the advanced configuration. Due to the diverse nature of RegEx, the rules are subject to timeout and automatic disabling in the event the crafted expression poses a risk to the stability of your VictorOps instance.
Some limitations to keep in mind:
- Expressions are currently limited to 128 characters
- There is a strong chance you will want to add (?si) to the beginning of your regex to match multiline input in a non-case-sensitive way.
- This will have to match the entire input string, so you may need to put .* on the beginning and end of your regex.
- Compatible with Java regular expressions
- We recommend using a RegEx validator like RegEx Planet to ensure proper syntax
Regular Expression Example
| Phrase | Matches | Does Not Match |
|---|---|---|
| ^\d+(\.\d+)? | 2 2.4 50 5.125 | b2.4 version 2.4 |
| ^\d{3}-\d{3}-\d{4}$ | 123-123-1234 111-222-3333 | number: 123-123-1234 123-123-1234 US |
| \w{2,} | ab abc abcd 123abcd abcd123 | 1 a1 1a |
| c(at|ar)? | cat car catalyst carbon a la carte | chart clark |
AND / OR Logic
OR logic can be achieved by simply replicating a rule with a different matching condition.
Using a set of sequential rules, when ordered correctly, can achieve basic AND logic in the Rules Engine. As with scope limiting rules, the first rule must create a new field which can be acted upon by a subsequent rule.
AND Logic Example
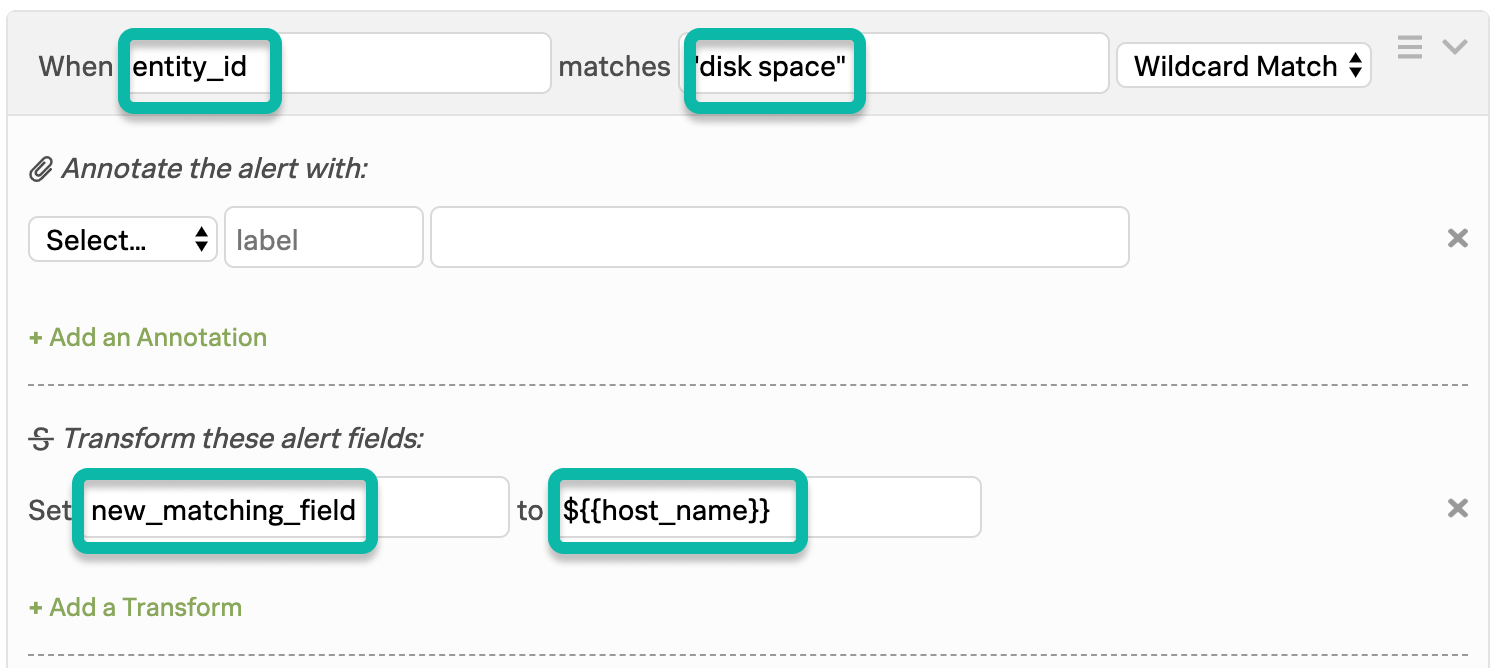
Let’s say you want to catch the phrase “disk space” from the entity_id field AND the name “stage-db-26” from the host_name field to convert these alerts to INFO events only when both these conditions are met.
The matching condition for the first rule will catch the first desired phrase and use variable expansion to import the value of the second field into a newly declared field.
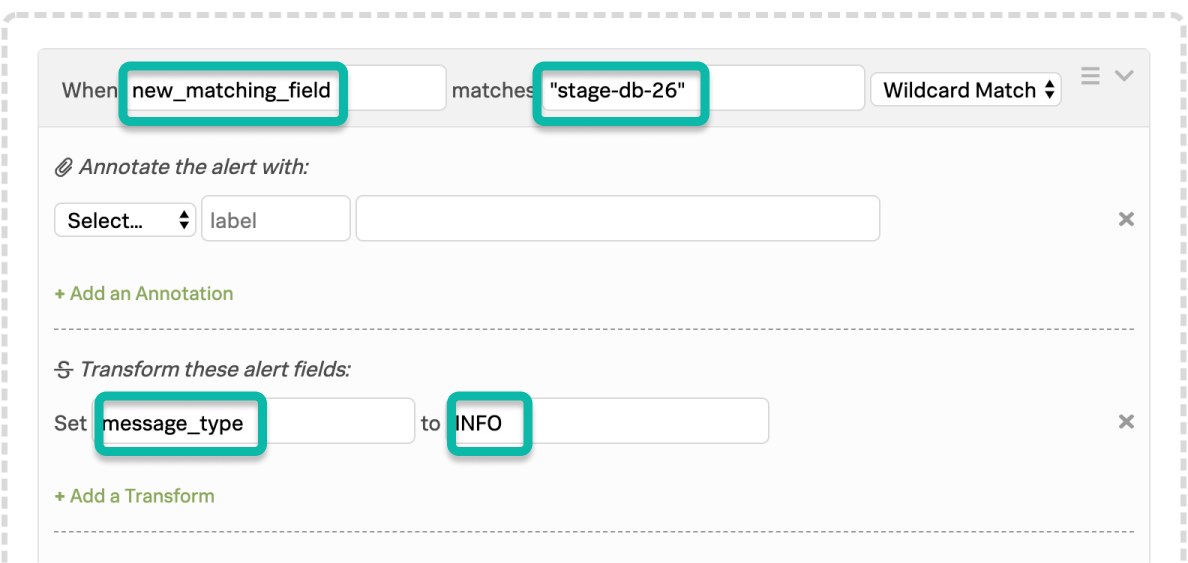
The matching condition for the second rule (MUST BE POSITIONED BELOW THE FIRST RULE!) checks the newly declared field for the value “stage-db-26” and takes the appropriate action.